I don’t like catching a virus or malware (in my Windows 7 PC) and neither do most people. I wasn’t thinking about an infection issue with my PC when I read about a new, free, open-source malware detection tool called Detekt. It is far more effective at detecting malware than my copy of Norton Internet Security. I downloaded it and let it run in Administrator mode after disconnecting from the internet. After two hours or longer, what it reported was scary.

Well, not immediately scary, because I had not heard of FinFisher FinSpy. The other two were annoying, because Norton Internet Security had not picked them up. FinFisher is an expensive set of hacking tools from Germany intended for governments with decent budgets. If you are infected with FinSpy, you have been individually targeted by some government police or intelligence agency.
Note: This might well have been a false positive, but I wanted to get rid of it all the same.
Also annoying was the lack of any instructions on how to remove this malware, but a suggestion to visit https://resistsurveillance.org/emergency, whose advice to disconnect the PC from the internet immediately and either dispose of the computer (!) or seek help from one of three people:
- nex@nex.sx
- eva@eff.org
- eric@privacy.org
Really? Are three people going to help thousands of people who discover they need help? I wrote to eva@eff.org because I was once a member of EFF and will see if I hear back. I also posted on the Norton Internet Security (NIS) forum to see if there is any solution from Symantec. EFF has some tips on avoiding malware, but it’s too basic for me.
Disposal of this PC was tempting, as it is seven years old and I could do with the excuse, but I also like solving problems. There isn’t anything helpful about removing FinSpy (that I could find), but I did see a comment that it needs Microsoft .NET Framework to work, so I removed it. (I found out later, that the automatic Windows Update setting installs it again!)
Table of Contents
Diagnosis and analysis
Malwarebytes
I was determined to solve this problem and couldn’t rely on NIS to do so, so I fired up Malwarebytes Free.

You will see that each of these scans took time, so most of my weekend was lost. No luck with this tool, so I did some Googling.
Norton Power Eraser
I read that Norton has this tool called Power Eraser. It found some dead wood and I got rid of those files. It found something called RestartNeroSetup. I don’t know how a Nero (disk burning) file could be a problem, but I removed it.

Norton Internet Security
I wasn’t satisfied that NIS hadn’t removed the minor malware, so I ran it manually with a Custom (Full System) scan. It got rid of the two files.

Anti-Malware Toolkit
After more searching, I found a download tool that has grouped a bunch of tools you can choose to download to assemble your own set of anti-malware tools. It detects what you have and what you don’t, then checks the files it thinks you will need.

SuperAntiSpyware
I tried this tool, not expecting it to know about FinSpy. It didn’t, but it found a problem in a file download “speeder-upper” that hasn’t been picked up by other tools in the past. It found Backdoor.Prorat – a Remote Access Trojan (RAT). It wasn’t a program I use, but I must have collected it at some time, so I was happy to lose it.

HiJackThis
If you visit self-help forums that cover malware or PC problems, you will often see people posting lengthy log files produced by a tool known as HiJackThis. I went through the log and looked up any file that I did not recognise. In particular, one entry stood out – Trusted Zone: http://software.kuaiche.com.

It didn’t look right, as I had no recollection of this site, which is in China. Some searching brought up a lot of malware discussions, but I kept looking and found this page. I remembered that I have Flashget, a file download helper. It was probably named to resemble a similar browser add-on called FlashGot. So I deleted FlashGet, even though it wasn’t running on my PC or browser. I went into the internet options and removed kuaiche.com from the Trusted Zone.

CCleaner
CCleaner is one of those housekeeping tools I use from time to time to clean up the registry and other debris that collects on a PC. I ran it and gained some space.
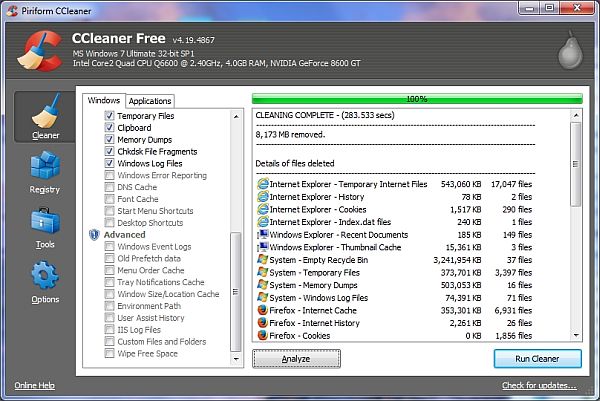
Of course, CCleaner didn’t help with the removal of FinSpy, but I was in a spring clean-up mood.
Back to Detekt
I thought I’d waste another couple of hours running Detekt and let it inspect my PC. Meanwhile, I thought I’d check my other PC that had been running it overnight. No problems on that PC. This is how the good news was reported:

Good for that PC, but mine still had the annoying FinSpy. Not surprised, as I hadn’t done anything special to look for it. I went to bed with the PC disconnected from the internet. During all this cleaning, I had to have the internet connected so that I could download the tools.
Windows Reliability Monitor
In the Windows search box, search for “View Reliability History”. This will open up the Reliabillity Monitor. It looks a little different in Windows 8 than the picture below. It lets you see the problems picked up on your PC. Nothing too useful for me.

Use your head, man!
At this point, I thought I should think outside the square and not keep looking for FinSpy solutions. Clearly, it has been in the wild for about one or two years but nobody has written a definite guide for removing it. I needed to solve this, or buy a new PC, which was looking very attractive at this point.
Reinstall Windows?
One of the generic malware solutions is to reinstall the operating system without affecting the rest of the PC. Since I have Windows 7 Ultimate on this machine and it has Service Pack 1, I needed to find out which DVD I had used back in 2011, on account of needing the correct key. I would need to remove Service Pack 1 before attempting a reinstall of Windows 7.
Speccy
I read that Speccy is one of many tools that shows you the software product key. I ran it and obtained the product key and located the Windows DVD.

However, Speccy also enables you to look at the live internet connections that are constantly going on – you’d be surprised how many programs and processes are connected to some remote site. A RAT needs to be connected with its control centre, so it is essential to view all such processes. I should have thought of this earlier, instead of looking for non-existent solutions.

Netstat
In passing, I should mention that the Windows Command Prompt also enables you to run the command “netstat -a” to see these processes.

Hetzner Online
I noticed the connections to 5.49.63.178 and used Whois to learn that it is some German ISP. I couldn’t think of any of my programs that needed to talk to a German site, so I decided to block it.
TCPView
Meanwhile, I read that TCPView is a great tool from Microsoft that shows you a lot of details about the internet connections I mentioned above. You can sort by any column and I like having the highest Local Port at the top of the screen, as it shows new processes that are just starting.

Router block
I went into my router’s Advanced Settings to the Outgoing Filtering screen and blocked that IP address. I went back to TCPView and right-clicked the entry to kill the processes (usually 4-5 of them). Not all of them would die through my efforts, but the router block did the trick.
Within seconds, the German site had a new IP address! So I blocked it, killed the processes and then a new one popped up. In the end, there were five addresses to block (All protocol = TCP; Port 443):
- 5.49.63.178
- 132.61.63.178
- 134.33.46.78
- 178.63.49.5
- 178.63.55.16
Finally, there were no connections to unknown destinations. The problem hadn’t gone, because if I have been personally targeted by some government agency, it would be trivial for them to assign some other IP addresses. No celebrations yet. Don’t assume that your infection will have those addresses.
Firefox add-ons are the culprit
Firefox is my preferred browser and I had 25-30 add-ons. I had read some old articles about how FinFisher masquerades as other programs, including Firefox, so people could install a browser that is actually malware.
I removed all add-ons and then unblocked the German IP addresses. No activity. I reinstalled some old and trusted add-ons. Still no activity. The culprit is one of the add-ons that I have not reinstalled. At least, that is my working assumption, as the malware has not resurfaced. I don’t have time to reinstall all of them to find the specific one, as not all were from Mozilla’s repository. If I find it, I will update this article.
Success

Keeping out of trouble
How can I keep FinSpy out of my PC? If I am targeted, then it will be impossible, but I will be a little more careful not to download add-ons that are not directly hosted by Mozilla. I will also keep TCPView running so as to see what remote addresses pop up in the active internet connections. If a strange one comes up in a set of 4-5 and won’t be killed, I will know that a new RAT has arrived and needs to be eliminated. Check all unknown IP addresses for their reputation at http://www.projecthoneypot.org. I will also run Detekt frequently.
Although I have cleaned up more than I needed to, it was a good exercise and time for reflection. Now I can see that my PC connects with LinkedIn, Microsoft Singapore, Symantec etc. Did you know that your PC acts as a relay for other people’s Skype sessions?
Summary
To summarise, you need three main tools in addition to your main malware/anti-virus defences:
- TCPView – to see internet connections to strange places and kill the processes
- Your router’s outbound filtering interface – to block strange IPs and see if a new one pops up in TCPView.
- Detekt
Good luck.
Agree that it might be a false positive, as I am not engaged in any questionable communications, but is that relevant when I simply want to get rid of it? Lots of people will hear about and run Detekt and will want to get rid of such positives, be they true or false.
Also agree that Detekt needs to come up with a better dialogue with its users when something is found.
Hi, I got the same response as you, Finspy plus the other two. You don’t mention the Detekt log file, anything interesting/useful in that?
In the log there are interesting, repeating text fragments, e.g. skyperec1, Jane.Dow’s.x32.machine, but can’t relate them to anything I know of.
Actually just spotted that the log file tells you which process the spyware appears to be running in, I stopped that process and deleted the associated exe, ran Detekt again and it was clean.
Oh? It was ipoint.exe in my case – part of Microsoft Mouse. It is still running now, but Detekt hasn’t complained since. Wonder if that Firefox add-on interacts with it to create the false positive?
Get a managed switch that allows spanning ports
Get a copy of some sort of bootable CD with a network stack (OpenBSD sounds good)
Set up the managed switch to span the port your router is on and the sniffer machine
sniff the traffic with some sort of packet sniffer. Filter in ingress/egress to your IP (better to use static IP’s behind a NAT’d router/firewall anyway…)
You could also just run an OpenBSD firewall between your network-router and run something like SNORT… make the file system immutable if you do.
Practice safe hex…